
Archives containing sensitive information can be encrypted for added security.
Old saying: Security is the opposite of convenience.
Before you add encryption to an archive, it's helpful to understand a little about how QRecall's encryption works.
When you add encryption to an archive, QRecall generates a random encryption key. This is a symmetric key, used both to encrypt and decrypt the data in your archive.
This encryption key is stored in a file called the encryption key file, or just key file. To access the archive (say, to browse and recall some items), QRecall reads the key file and uses the encryption key to decrypt the archive:

The encryption key file is stored in your home folder
(specifically in ~/Library/Application Support/QRecall/Keys).
Because the key file and archive aren't normally stored on the same volume,
an agent that has access to just the archive can't access any of its data.
An agent that has access to both the archive and a computer system containing the key file could, however, access the data. To add an additional layer of security, the encryption key file can, itself, be encrypted with a password. Accessing the archive now requires the archive, the encryption key file, and the encryption key's password:

The encryption key password can be entered every time you need to access that archive, or it can be stored on your keychain for automatic retrieval.
To encrypt your data, open the archive and choose ➤ ➤ .
To encrypt future data added to an archive:
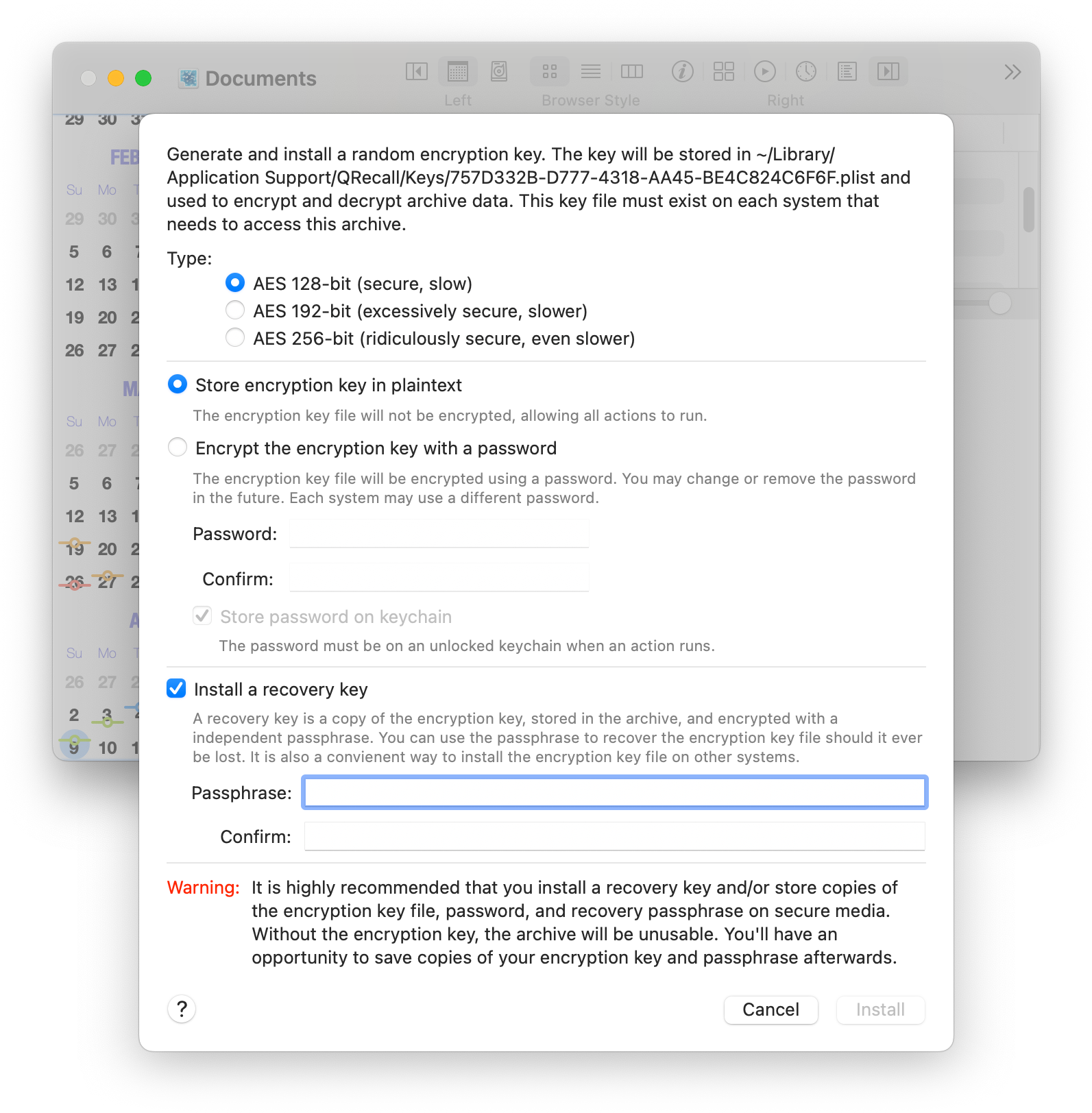
First, choose a key length. QRecall uses the Advanced Encryption Standard (AES). A 128-bit key is more than adequate for most purposes, but you also have the choice of 192-bit and 256-bit key lengths for situations that demand it (government or company policy compliance, for example).
As mentioned earlier, the encryption key file can be encrypted with a password. You may elect to do this if your computer is not physically secure, although this will complicate access to the archive.
To encrypt the key file, choose Encrypt the encryption key with a password and enter a password, twice to confirm. You may optionally choose to add the password to the keychain now. Either, or both, of these steps can be done (or undone) later.
Automated actions must have access to the encryption key in order to function.
This is easiest when the encryption key is not password protected; all QRecall actions and command will have unfettered access to the archive using the encryption key file.
If the key file is password protected, and the password is saved on the keychain, each action will first have to retrieve the password from the keychain. This requires that you be logged into your account with your keychain unlocked.
If the password is on the keychain, but the keychain is locked, the action will prompt for keychain access. If the password is not stored on the keychain, or you are not logged in, the action will fail.
The strength of any security is its weakest link.
The random encryption keys generated by QRecall are as secure as it gets. If you can prevent an agent from gaining access to the encryption key, your archive data is completely safe.
If you protect your encryption key with a password, the strength of your security becomes the strength of that password; strong encryption protected by a weak password is the same as weak encryption.
Note: the pass key used to encode the encryption key file is salted. This makes it resistant to most key cracking algorithms, but does not make it immune to well-known password dictionary attacks. In other words, don't use “123456” as your password or passphrase.
Similarly, if your strong password is stored on the keychain, and your keychain password is weak, that becomes your security's most vulnerable point.
A recovery key is a copy of the encryption key, encrypted with a passphrase, and stored in the archive. A recovery key acts as an emergency backup for your encryption key and makes it easy to retrieve the key, should you need it. Installing a recovery key is highly recommended.
While technically identical to a password, a passphrase should be longer and harder to guess, often an entire sentence. Enter it twice to confirm.
Once everything is set up, click the Install button to install the encryption key.
A dialog will now appear prompting you to make backup copies of your encryption key file and/or the passphrase used to protect your recovery key.
The importance of keeping backups of your encryption key cannot be stressed enough.
QRecall uses completely random (maximum entropy) AES encryption keys. This level of encryption is considered unbreakable by modern standards, even by governments with massive resources. There are no known hacks, key crackers, or backdoors.
If you lose the encryption key, your archive data will be lost. Period. End of Story. No exceptions.
Do not call me in the middle of the night, crying into the phone, that you've lost your entire life's work because your hard drive crashed and you lost your encryption key file. I can't help you. No one can.
The same is true for password protected encryption key files and recovery keys, it's equally important to keep track of those passwords and passphrases.
If you didn't create a recovery key, making a backup of your encryption key is strenuously encouraged. Please, I'm begging you; make a backup! If you protected the encryption key file with a password, the backup will be protected by the same password. (Don't lose that either!)
If you elected to install a recovery key, it's equally important to keep track of your passphrase. Checking the passphrase backup option will prompt you save the passphrase as a file; you can later use that file to reload the passphrase, without having to type it in.
The backups of your encryption key and password/passphrase file(s) should be kept on enduring media in a secure location, separate from both your computer system and the archive storage.
All digital media has a shelf life, so be aware of its limitation when crafting an encryption key backup strategy. Here are some suggestions:
The backup files you create during installation can also be used to provide the encryption key or passphrase when using the command line tool.
See the --keyfile, --password, and --passphrase options
in man qrecall for the details.
The encryption key will by applied to all new data added to the archive.
If you just added an encryption key to an existing archive containing sensitive data, choose the ➤ ➤ command to immediately apply the encryption to all unencrypted data.
Because the archive's encryption key is not based on a password, it's possible to change (or remove) the password that protects the encryption key file.
Choose ➤ ➤ to set, change, or remove the password protecting the encryption key file.
If the key file is not currently password protected, you'll be prompted to enter a password and optionally add it to the keychain.
If the key file is already protected by a password, you'll see a dialog requiring you to enter the existing password. You'll then have choices for removing or changing the password:
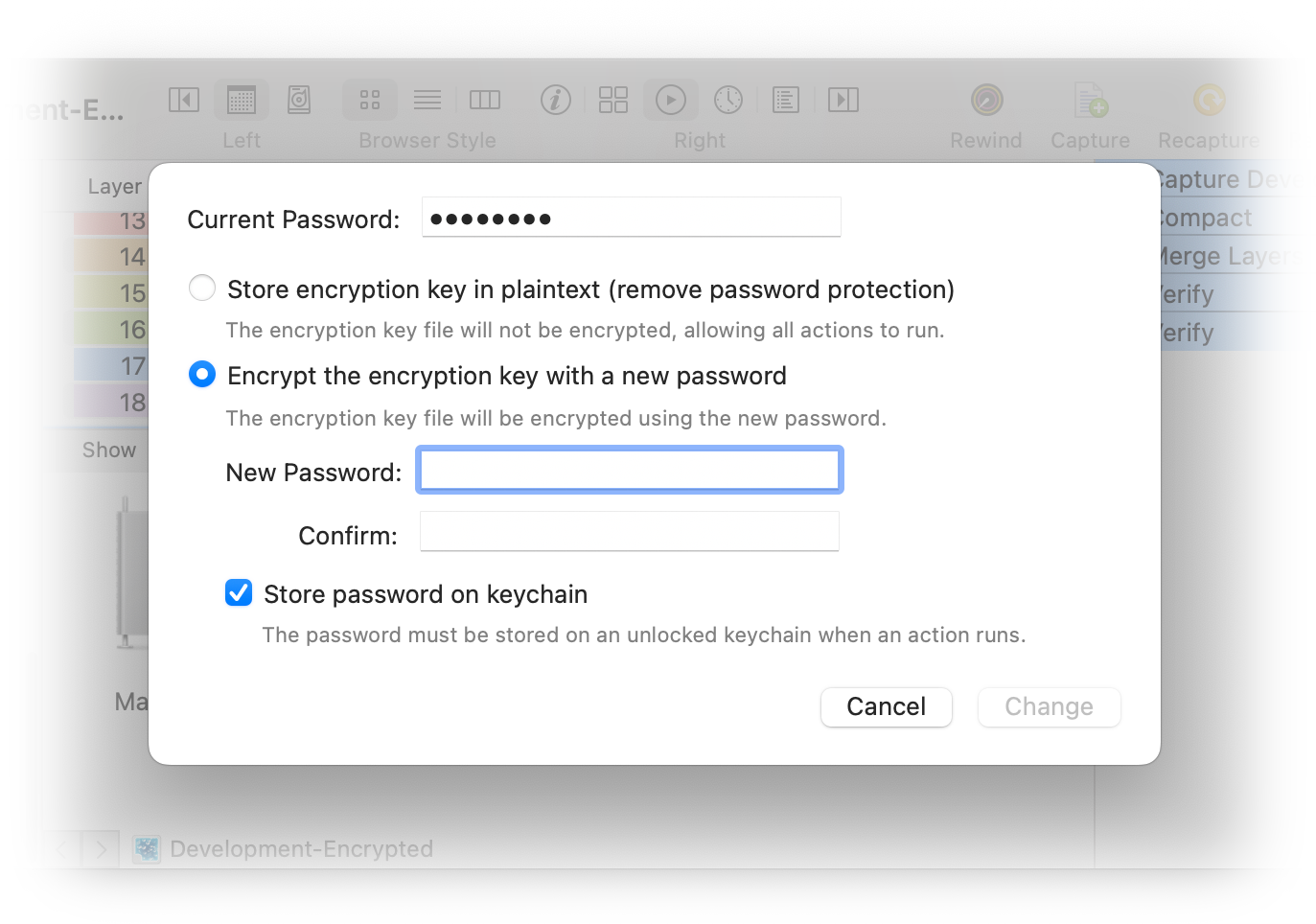
Each system can have a different (or no) password, and that password can be changed independently of any other system using the same archive. See Encrypted Archives and Multiple Systems.
The one exception is when you import a backup key file or copy an existing key file from another system. If the imported/copied key file is protected with a password, the installed copy will be protected by the original password—which you are then free to change.
If you (went temporarily insane and) elected not to add a recovery key to your archive when setting up encryption, you can correct that oversight at any time by choosing the ➤ ➤ command. You'll be prompted for a passphrase, which you should save someplace safe.
If you (decide life would be more exciting knowing you could lose all of your data and) want to remove the recovery key, hold down the Option key and choose the ➤ ➤ command.
There is no direct way to change the passphrase used to protect the recovery key.
If you need to change the passphrase (possibly because you lost the old one), remove the existing recovery key and then reinstall it using a new passphrase.
Key recovery is invoked automatically, as needed.
If you open an archive and QRecall cannot read the encryption key file for that archive, and the archive contains a recovery key, you'll be prompted to enter the passphrase for the recovery key. The encryption key will be decoded and reinstalled.
If you want to remove encryption, open the archive, hold down the Option key, and choose the ➤ ➤ command.
This command will use the installed encryption key to decrypt all protected data in the archive and rewrite it in its unencrypted (plaintext) form. The command then uninstalls the archive's encryption key.
You must decrypt an archive before installing a new encryption key, something you might want to do if the security of the existing encryption key has been compromised.
You can freely rename or relocate encrypted archives. QRecall will detect this and automatically update the binding between the archive and its encryption key file.
As a rule, you should not make a copy of an encrypted archive. If you do, you'll end up with multiple archives that depend on a single encryption key file. This can be the source of some confusion, possibly data loss.
If you need to duplicate an encrypted archive, and intend to use it independently of the original, you should:
If you access an encrypted archive from multiple computers, you must install that archive's encryption key on each system.
The easiest technique, by far, is to install a recovery key in the archive and use that recovery key to install the encryption key on each system that needs access to it.
If you don't want to install a recovery key, you can use the same basic technique using the backup of the encryption key file you made during installation. If the archive lacks a recovery key, attempting to open it without an encryption key installed will present an option to import the backup encryption key file. Select Import and navigate to the backup copy.
If you don't have either a recovery key or a backup copy of the key file, you'll have to locate the installed encryption key file on the original system and make a copy of it.
Encryption key files are located in the ~/Library/Application Support/QRecall/Keys folder.
To find the key file for a particular archive:
Alternatively, issue the qrecall keys check command in the Terminal.
Search the output for the key file that belongs to the archive.